Worse than Frenemies
October 22, 2015 •Walt Paley
You've heard the term 'frenemies' before, right? You most likely have if you've got kids past middle school, unfortunately. It's the mash-up of 'friend' and 'enemy' with the distinction defined in the helpful illustration below.
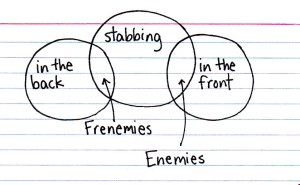
Today's blog post is a public service announcement - Beware of frenemies. Many of us forget about this life lesson once we are adults and it can really sting. Frenemies come in several flavors in the business world, but many are friend/competitors. Maybe these should be called 'frempetitors'.
Our prime example is Samsung and Apple. They have been engaged in litigation since 2011, and yet Tim Cook's braintrust thought it was a good idea to contract with Samsung to produce A9 processors for the iPhone 6S. Samsung was even accused of engaging in corporate espionage to displace TSMC, who had been slated for the full order. Even the most forgiving folks would have to be a little suspicious, right?
Now the kicker - Samsung's version of the A9 chip has been benchmarked for worse heat dissipation and shorter battery life than the alternative version by TSMC. Was this malicious? Was Samsung actively trying to undermine the reputation of Apple's new flagship phone? Popular Apple-centric blog 'Cult of Mac' says maybe they are. The fact that the two corporate giants have been locked in mortal combat in both the courtroom and for market share automatically throws a shadow on the developing situation. Despite Apple's public claims that the variance is only 2-3% and it won't affect typical use, Samsung doesn't get the benefit of the doubt, since they are the very definition of 'frempetitors'. I'd love to hear the internal discussions in Cupertino on the topic.
So why do you care? Well, we've had a spike lately in inquiries from companies in a specific industry that have been using an encryption product from their frempetitor. Yes, they licensed a crypto module from [company name redacted] even though they are competing head-to-head against that company's flagship product. This boggles my mind. We're not talking about complementary offerings, we're talking about the exact same kind of Apple-Samsung clash of the titans but on a smaller battlefield. Why would you trust this frempetitor? It's not like their product is so fantastic that you had no choice. It's certainly not that their pricing was so incredible that you couldn't afford to pass it up. For comparison's sake, it's not even like they provide FIPS 140-2 validation services, Rapid or otherwise. This is just a head-scratcher.
What happens when their module isn't working properly or if it is proven to be vulnerable? Will they step up and patch it in a timely manner? Or will they prioritize their own products and customers first, and you'll have to wait until they get around to it?
What if your crypto provider pulls your license in an effort to sidetrack your engineering team and cripple your momentum, because you've been taking market share from their primary offering? Are you prepared to pivot quickly on your competitor's whim?
Would you be concerned that you are relying upon an internal component that was designed by a competitor? What if it slows down your product's performance? What if it includes tracking capabilities so that they can monitor your install base?
Paranoid? Sure, but definitely within the realm of possible.
If you ran a restaurant, you would never purchase your ingredients from a competitive restaurant. You'd rightfully assume that they would cherrypick the best produce, the best cuts of meat, the proverbial cream of the crop, and leave you the rest.
Would your boss/investors/shareholders/customers give you the benefit of the doubt in these scenarios? Is choosing to work with a frempetitor ever a justifiable position in retrospect?
Skip the heartache and paranoia. Don't get stabbed in the back and don't give a competitor the opportunity to be a part of your supply chain.
If you are currently using encryption provided by a company that would stand to gain from your troubles, contact us immediately and we'll help you escape from this dysfunctional relationship. If you are considering them, please think very carefully about it before you move forward. I don't promise never to say "I told you so", but I do promise that SafeLogic will be ready to help when you're ready. Plus, we have better modules, greater compatibility and platform coverage, and RapidCert's lightning fast validation is just the cherry on top. Choose wisely!

Walt Paley
Walter Paley is the VP of Communications for SafeLogic. He is responsible for strategy, content, marketing, and outreach. Walt has worked with a series of start-ups and companies in growth stages, including Nukona (acquired by Symantec), Qubole, Bitzer Mobile (acquired by Oracle), and TigerText, among others. An Alumnus of the psychology program at UC San Diego, Walt lives in Southern California with his wife, kids, and their black lab, Echo.
Search for posts
Tags
- FIPS 140 (115)
- FIPS validation (85)
- Encryption (69)
- cryptography (67)
- NIST (62)
- CryptoComply (60)
- SafeLogic (57)
- Industry News (52)
- cryptographic module (51)
- CMVP (48)
- Conversations (47)
- RapidCert (46)
- compliance (40)
- Ray Potter (33)
- SafeLogic News (32)
- Event (26)
- federal (26)
- CAVP (24)
- Cybersecurity (23)
- FIPS 140-3 (22)
- post-quantum cryptography (18)
- PQC (17)
- FedRAMP (15)
- OpenSSL (15)
- government (14)
- CryptoCompact (12)
- Cryptology (12)
- DoD (12)
- healthcare (12)
- partners (11)
- RSA (10)
- Cloud (9)
- NSA (9)
- CMMC (8)
- Suite B (8)
- security (8)
- whitepaper (8)
- testing (7)
- Approved Products List (APL) (6)
- HITECH (6)
- ICMC (6)
- NIST 800-53 (6)
- CEO (5)
- Entropy Source Validation (5)
- NIST 800-171 (5)
- OpenSSL 3.0 (5)
- iOS (5)
- lab (5)
- procurement (5)
- C3PAO (4)
- Common Criteria (4)
- HITECH Act (4)
- OpenSSL 3.x (4)
- TLS 1.3 (4)
- entropy (4)
- innovation (4)
- procure (4)
- Air Force (3)
- DFARS (3)
- HIPAA Safe Harbor (3)
- HITECH Safe Harbor (3)
- OpenSSL 1.1.1 (3)
- POA&M (3)
- deadline (3)
- encrypt (3)
- magazine (3)
- public sector (3)
- queue (3)
- ACVP (2)
- BAA (2)
- BSAFE (2)
- CIO (2)
- CSP (2)
- Defense Industrial Base (2)
- FISMA (2)
- HIPAA security controls (2)
- Historical Status (2)
- MFA (2)
- OpenSSL 1.0.2 (2)
- SPRS (2)
- StateRAMP (2)
- excellence (2)
- founder (2)
- gold (2)
- leader (2)
- maturity (2)
- pilot (2)
- rsa conference (2)
- solution (2)
- transition (2)
- year (2)
- 3PAO (1)
- Active Status (1)
- Alliance for Digital Innovation (1)
- Android (1)
- CIO Prime Views (1)
- Cyber Defense Magazine (1)
- DHS (1)
- DIU (1)
- DIUx (1)
- DOJ (1)
- DoDIN APL (1)
- FCA (1)
- FIPS Compliance (1)
- GSA (1)
- HITRUST (1)
- Matt Cornelius (1)
- Matthew Cornelius (1)
- Maturity Model (1)
- NCCoE (1)
- OMB (1)
- OpenSSL 3.5 (1)
- SLED (1)
- SP800-131A (1)
- SP800-90A (1)
- TLS 1.1 (1)
- background (1)
- best (1)
- co-founder (1)
- congress (1)
- cybertech (1)
- education (1)
- elliptic curve cryptography (1)
- faq (1)
- finance (1)
- fintech (1)
- fiscal (1)
- fiscal year (1)
- fraud (1)
- globee (1)
- hill (1)
- interview (1)
- kratos (1)
- libgcrypt (1)
- national cybersecurity strategy (1)
- opportunities (1)
- overlap (1)
- parallel (1)
- profile (1)
- representatives (1)
- reseller (1)
- senate (1)
- senators (1)
- simplify (1)
- sponsors (1)
- stealth mode (1)
- story (1)
- sunset (1)
- vendor (1)

