Important News:SafeLogic Announces General Availability of CryptoComply BoringCrypto! Read the announcement.
Cryptography and Encryption for Healthcare Organizations
Cryptography is Ubiquitous, Critical, and Highly Regulated
-
Cryptography is everywhere. It is a key security control that enables privacy, security, and trust in our digital world. As a result, it is more highly regulated and subject to extensive implementation testing than perhaps any other security control
-
NIST's FIPS 140 standard dates back to 2001 and specifies extensive laboratory testing and certification for cryptography implementations sold to the US government
-
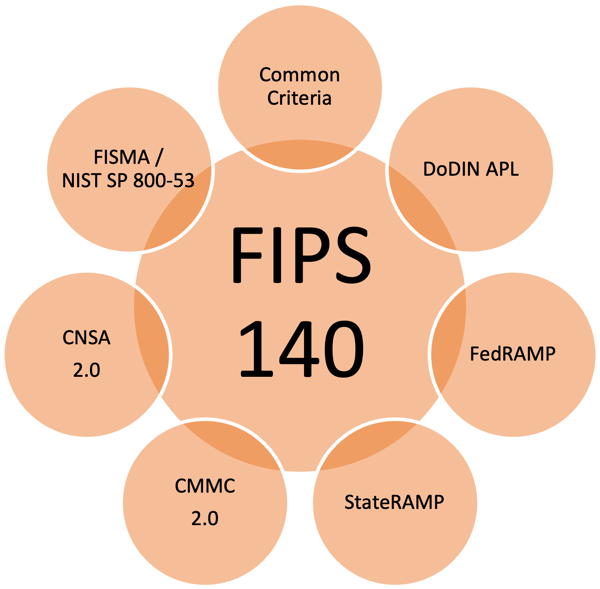
Numerous additional government security standards and frameworks, including FISMA, NIST SP 800-53, Common Criteria, DoDIN APL, FedRAMP, StateRAMP, CMMC 2.0, and CNSA 2.0, have all adopted FIPS 140 as the gold standard for cryptography compliance
HIPAA and HITECH Regulations for the Protection of Electronic Personal Health Information Validate FIPS 140

-
HIPAA, the HIPPA Privacy Rule, the HIPAA Security Rule and HITECH define requirements for the protection of electronic protected health information (PHI) when at rest and in motion. These security regulations, breach notification requirements and breach penalties apply to all covered organizations and their business associates
-
While these regulations attempt to be non-technology-specific and as a result can be confusing, the HITECH Breach Notification for Unsecured Protected Health Information rule specifically references NIST’s FIPS 140 certification of encryption products as meeting its requirements for Safe Harbor against breach notification and penalty requirements.
-
As a result of this and other references, FIPS 140 certification has become a de facto standard for technology products used by covered organizations and their business associates that perform encryption operations on PHI
Classical Cryptography is Under Threat from the Emergence of Quantum Computers
-
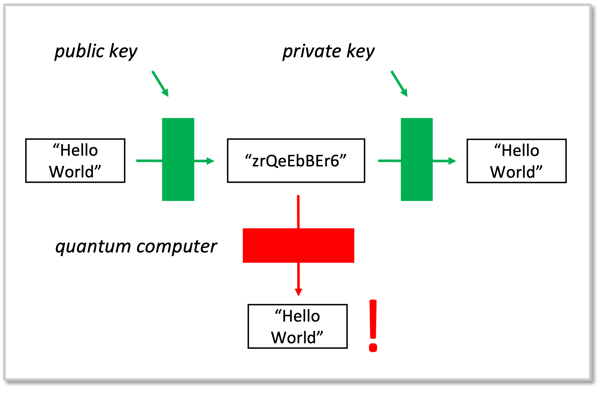
Asymmetric (public/private key) cryptography has been used in almost every aspect of computer security for 30 years
-
Classical PKI algorithms rely on mathematical problems existing computers cannot easily solve, but emerging quantum computers will solve easily
-
Gartner predicts quantum computing will make existing systems unsafe to use cryptographically by 2029
-
Cryptographic products and services will need to be updated or replaced to use post-quantum cryptographic (PQC) algorithms to protect against this threat
-
NIST is standardizing PQC algorithms in the summer of 2024 after an extensive 5+ year evaluation process. Once standardized, they will be added to FIPS 140
Even Without Quantum Computers Today, 'Harvest Now, Decrypt Later' is Already a Critical Threat to the Healthcare Industry
-
In the realm of cybersecurity, the "Harvest Now, Decrypt Later" (HNDL) threat has emerged as a significant concern, particularly for the healthcare sector
-
This nefarious strategy involves adversaries collecting encrypted data today in anticipation of decrypting it in the future, once quantum computing capabilities mature
-
The healthcare sector is rich with sensitive data, making it an attractive target for HNDL attacks.
-
There are five reasons why the healthcare industry must be particularly vigilant: highly sensitive data, regulatory compliance, long-term data value, the potential for operational disruption, and R&D and proprietary information
-
This looming threat underscores the urgent need for healthcare providers and vendors to adopt robust, quantum-resistant cryptographic measures

SafeLogic is an Ideal Strategic Cryptography Software and Services Partner for Healthcare Organizations

Healthcare organizations including payors, providers, medical device makers, pharmaceutical manufacturers, and government agencies face daunting requirements for next-generation cryptography: comprehensive solutions that interoperate with their entire tech stack, manageable deployability both now and in the future as the world transitions to post-quantum cryptography, and compliance with ever-changing regulatory frameworks starting with the transition to FIPS 140-3.
Trusted by many of the world's top firms, SafeLogic expedites and streamlines the adoption of FIPS 140-validated classical and post-quantum cryptography.
Our holistic and interoperable cryptographic solutions save our customers time, effort, and money while ensuring their use of the strongest cryptography available.
With our FIPS 140 Validation-as-a-Service, companies can get a FIPS 140 certificate in their name in two months versus the two-plus years the process normally takes.
In addition, SafeLogic customers are already testing PQC algorithms and techniques as NIST finalizes its initial PQC standardization efforts.
SafeLogic is Excited to be Partnering with Altus, a Leading Provider of Computer Workstations for the Healthcare Industry
-
With more than 20 years of combining ergonomics and mobility, Altus is continuously innovating new ideas to design workstations built specifically to improve healthcare workflows and improve clinician comfort. Each medical-grade cart is engineered to offer the most ergonomic design possible. With options in mobile computer carts, telehealth carts, and wall-mounted workstations, there is a solution to improve any workflow
-
Altus has been working behind the scenes on #cybersecurity compliance with its forthcoming fleet management and IoT-enabled workstations. FISMA, HIPAA and HITECH healthcare regulations require FIPS 140 validation for any cryptography deployed within the solution
-
By partnering with SafeLogic, Altus has recently received FIPS 140-2 certificate #4659 from NIST, which verifies that its specific in-development module has been validated. The module ensures secured data transfer using an encrypted protocol between carts, workstations, and web servers