Important News:SafeLogic Announces General Availability of CryptoComply BoringCrypto! Read the announcement.
January 14, 2016 •Mark Minnoch
Important News:SafeLogic Announces General Availability of CryptoComply BoringCrypto! Read the announcement.
Search
Key Capabilities
January 14, 2016 •Mark Minnoch
Question: I'm hearing rumors that my FIPS 140-2 cryptographic module will be moved to NIST’s Legacy Validation List on January 31, 2016. Is this true?
Answer: The rumors are true for many organizations, unfortunately. If your cryptographic module contains any of the RNGs in FIPS 186-2, ANS X9.31, or ANS X.9.62-1998 on the “FIPS Approved algorithm” list, your certificate will be re-classified and moved to the Legacy Validation List unless it is reaffirmed otherwise. In addition, certificates that have not been updated since 2011 or prior will be relegated to the Legacy List next year, as part of a five year rolling expiration. More on that soon.
The bad news: Federal agencies have been instructed to strictly avoid products that have been moved to this Legacy Validation List. We know that DISA has already contacted technology vendors that are in danger of having their certificates moved to the Legacy Validation List. This is a demonstration of DISA's attention to this issue - they plan to be extremely proactive and solutions that fall out of compliance will not be able to slide under the radar. Every vendor with an RNG included on their FIPS certificate should immediately take action to keep their modules available for procurement.
NIST Special Publication 800-131A has been warning that these RNGs will be “disallowed” in 2016. The SP800-131A publication contains guidance for the use of stronger cryptographic keys and more robust algorithms. Concerns of increasing computing power and possible new attacks, the older RNGs have been dropped by the NIST Cryptographic Technology Group in favor of the newer SP800-90A DRBG algorithms: HASH_DRBG, HMAC_DRBG and CTR_DRBG. Since randomness in generating keying material is essential to strong cryptography, this is a proactive step by NIST to evolve to stronger security solutions for federal agencies.
The good news: SafeLogic customers will not be affected. Our clients will remain on NIST’s Active Validation Lists. Federal agencies will still be allowed to acquire products that are using SafeLogic’s cryptographic modules when enforcement begins on January 31, 2016, due to our strong support team and aggressive updates to ensure compliance. SafeLogic's dedication to certificate maintenance has saved our customers significant time, effort and heartache. With NIST's renewed commitment to keeping the validation list current, maintenance is more crucial than ever before. Neglecting your certificate can quickly render obsolete the product of years of work and significant investment - and that's never a good thing.
Whether you have questions about the RNG transition, want more information on SafeLogic’s drop-in FIPS solutions, or your current validation is being re-classified to the archive list, please contact us. SafeLogic can help!
Now that you know SafeLogic can take care of your FIPS cert, here's some RNG humor to help dissipate that stress:
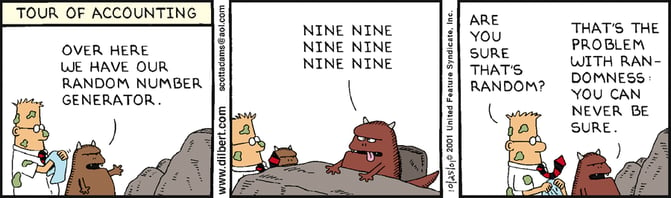 Classic Dilbert from 2001.
Classic Dilbert from 2001.

Mark Minnoch was a Technical Account Manager for SafeLogic.